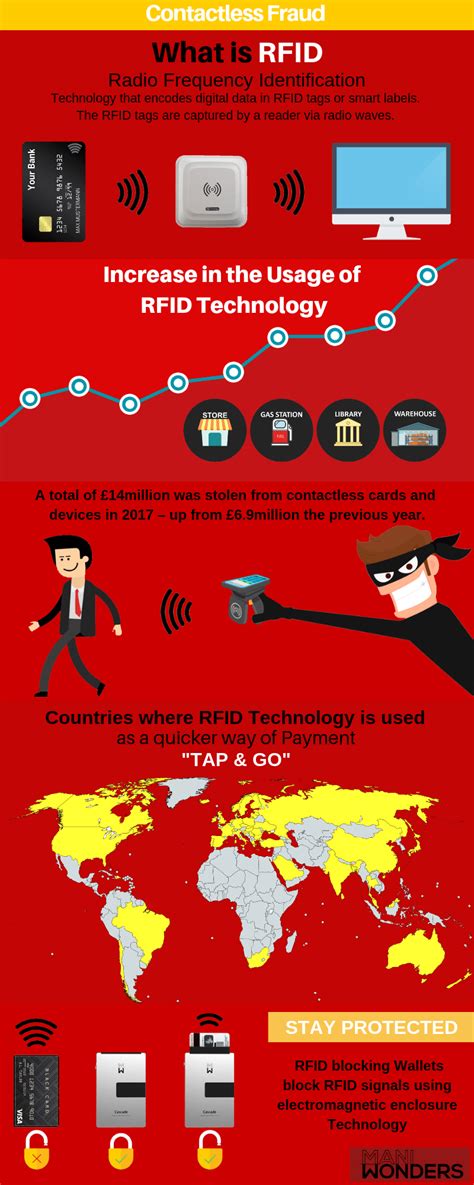
hack rfid card Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!
Zebra ID 카드 프린터는 결제용 카드부터 직원 ID 배지와 운전면허증까지 모든 .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hack tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid signal
Basically, I want to create a POC using Apple Wallet -> read a card using an RFID reader -> .
The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala. Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC . Step-by-Step Tutorial: How to Copy or Clone Access Cards and Key Fobs. Access credentials are prone to hacking. This post explains how easy it is to copy access cards with .
The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and .
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and .
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. 1. Proxmark3 ID DEV Kit. 2. Flipper Zero. 3. Keysy RFID Duplicator. 4. ESP RFID Tool. 5. LONG RANGE RFID READER / WRITER DL533N XL. Frequently Asked Questions. . The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the . Ever wondered how easy it is to hack an RFID card? In this blog, I’ll show you the basics of RFID technology and how to clone a card using tools like Proxmark3 and MIFARE .
rfid scammers
Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. .NFC-Hacking. This project showcases how to exploit vulnerabilities in NFC cards using Arduino and RFID technology. By leveraging the MFRC522 RFID module, you can read and write data . Step-by-Step Tutorial: How to Copy or Clone Access Cards and Key Fobs. Access credentials are prone to hacking. This post explains how easy it is to copy access cards with .
The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and . Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and . Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
1. Proxmark3 ID DEV Kit. 2. Flipper Zero. 3. Keysy RFID Duplicator. 4. ESP RFID Tool. 5. LONG RANGE RFID READER / WRITER DL533N XL. Frequently Asked Questions. .
The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the .
Ever wondered how easy it is to hack an RFID card? In this blog, I’ll show you the basics of RFID technology and how to clone a card using tools like Proxmark3 and MIFARE . Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. .
dense rfid tags
diy read delta rfid baggage tag
rfid scam
rfid how to block
NFC payments are contactless payments that use near-field communication (NFC) technology to exchange data between readers and payment devices—like Apple Pay and Google Pay e-wallets in smartphones and wearables or tap-to-pay credit and debit cards.
hack rfid card|rfid how to block