encrypted rfid reader How would you use symmetric cryptography? The card cannot trust the reader (any reader can be used for tampering) and the reader can certainly not trust the card. You could even perform a man-in-the-middle attack with specialist devices. Opens in a new window twitter for Football; . Fans can listen to free, live streaming audio of Auburn Sports Network radio broadcasts of Tiger games and coach's shows. Computer; Mobile App;
0 · types of rfid readers
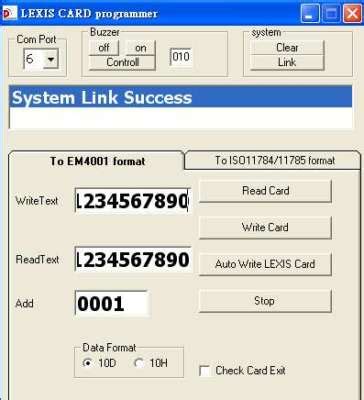
1 · rfid readers for sale
2 · rfid reader software windows 10
3 · rfid reader software download
4 · rfid reader meaning
5 · rfid reader function
6 · rfid reader for computer
7 · rfid label reader free online
To satisfy the growing popularity of the Ham Radio hobby, the Northeastern Indiana Amateur Radio Club will sponsor free classes leading to the exam for an FCC .A list of AM and FM radio stations near the city of Auburn, Indiana. Callsign: Zip code: City : State: Toggle navigation. Radio News; Radio Markets . Search; Location Search. Auburn, Indiana Radio Stations. We found 83 FM radio stations and 29 AM radio stations in the .
How would you use symmetric cryptography? The card cannot trust the reader .About this item. 1, Working Frequency: the working frequency of this card duplicator is 125KHz .
How would you use symmetric cryptography? The card cannot trust the reader (any reader can be used for tampering) and the reader can certainly not trust the card. You could even perform a man-in-the-middle attack with specialist devices.RFID tag encryption is a security technology used to protect data transmitted via radio frequency identification (RFID) technology. The main purpose of RFID tag encryption is to ensure that the data transmitted between the tag and the reader is not read or .
The remaining methods all rely on some form of encryption, so that the tag and reader can communicate in a way that is indecipherable to outsiders. Since these security measures are encrypted within the tags themselves, they require less effort from the people operating them. If there’s a need for encryption between the RFID media and the reader, the appropriate credentials are required. There are use cases wherein smart cards or passports store personal information such as name, address, date-of-birth or biometric data.
Learn about the authentication and encryption schemes that RFID readers use to communicate with RFID tags securely and privately.ARC-A is a secure and vandal proof RFID card reader. The most awarded access control reader around the world.
An MITM attack against an RFID system uses a hardware device to capture and decode the RFID signal between the victim’s card and a card reader. The malicious device then decodes the information and transmits it to the attacker so they can replay the code and gain access to the building.
To address this, various advanced encryption technologies have been applied to RFID chips to prevent data breaches and unauthorized access. This article will explore these encryption technologies in detail and introduce several well-known .The Mifare Ultralight C uses the Triple Data Encryption Standard (3DES) authentication method to secure communication between the card and the reader. 3DES is a symmetric-key encryption algorithm that uses a 56-bit key to encrypt and decrypt data. The 3DES authentication process involves three steps: Since systems often use the UID as an access measure, hackers can obtain the UID (or keys in the case of broken encryption) by reading existing cards from users and writing that UID to a new card or by simulating it with a device to a reader. How would you use symmetric cryptography? The card cannot trust the reader (any reader can be used for tampering) and the reader can certainly not trust the card. You could even perform a man-in-the-middle attack with specialist devices.
RFID tag encryption is a security technology used to protect data transmitted via radio frequency identification (RFID) technology. The main purpose of RFID tag encryption is to ensure that the data transmitted between the tag and the reader is not read or .

exxonmobil smart card pin
types of rfid readers

The remaining methods all rely on some form of encryption, so that the tag and reader can communicate in a way that is indecipherable to outsiders. Since these security measures are encrypted within the tags themselves, they require less effort from the people operating them. If there’s a need for encryption between the RFID media and the reader, the appropriate credentials are required. There are use cases wherein smart cards or passports store personal information such as name, address, date-of-birth or biometric data.
Learn about the authentication and encryption schemes that RFID readers use to communicate with RFID tags securely and privately.ARC-A is a secure and vandal proof RFID card reader. The most awarded access control reader around the world. An MITM attack against an RFID system uses a hardware device to capture and decode the RFID signal between the victim’s card and a card reader. The malicious device then decodes the information and transmits it to the attacker so they can replay the code and gain access to the building.
To address this, various advanced encryption technologies have been applied to RFID chips to prevent data breaches and unauthorized access. This article will explore these encryption technologies in detail and introduce several well-known .
The Mifare Ultralight C uses the Triple Data Encryption Standard (3DES) authentication method to secure communication between the card and the reader. 3DES is a symmetric-key encryption algorithm that uses a 56-bit key to encrypt and decrypt data. The 3DES authentication process involves three steps:
rfid readers for sale
features of smart card pdf
KSR Women's Basketball Kentucky WBB beats No. 18 Louisville 71-61 in overtime in Battle of the Bluegrass. KSR Football Cutter Boley Gained Confidence in Kroger Field Debut. University of Kentucky Sports News in the most .
encrypted rfid reader|rfid reader function