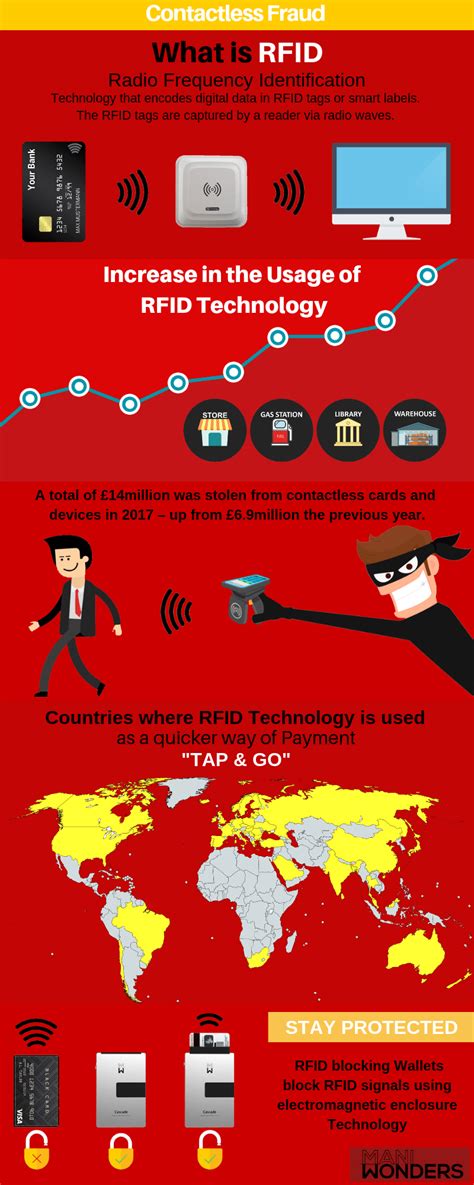
rfid access card hack RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos . Green Bay Packers 20 at Arizona Cardinals 26 on January 16th, 2016 - Full team and player .In honor of Free Game Friday relive the full game of Steve Young & the 49ers' emotional playoff win over Brett Favre and the Green Bay Packers in the 1998 NF.
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hack tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid signal
Contactless payment is a secure payment method using a debit or credit card, smartcard, or another payment device by using RFID technology and near-field communication. To use the system, a .Credit and debit card products tailored to your needs. Credit card; Debit card; Virtual Card; The Si debit card . Easy to use, internationally approved, NFC technology card for children and young people aged 7-22. Validity. 4 YEARS. Compare Apply . With American Express® Green Card .
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and . RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos .
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and can sniff and log. RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards. The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the Swiss lock maker.
Step-by-Step Tutorial: How to Copy or Clone Access Cards and Key Fobs Access credentials are prone to hacking. This post explains how easy it is to copy access cards with Flipper Zero, off-the-shelf hardware, and an app. 10 min reading time Hacker Tool Teaches All About NFC And RFID. The Flipper Zero is a multipurpose hacker tool that aims to make the world of hardware hacking more accessible with a slick design, wide array of . As detailed in the report, the security vulnerability allows “card-only” attacks, requiring access only to a card and not the corresponding card reader. The hackers can read and write data in just a few minutes of physical proximity .
There are many access control systems that rely on UID to authenticate and grant access. Sometimes this happens even when RFID tags support cryptography . Such misuse brings them down to the level of the dumb 125 kHz cards in terms of security . In their popular talk at 24C3, punctuated by bursts of raucous applause, Nohl presented an overview of radio frequency identification security vulnerabilities and the process of hacking the. Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. Some tags are passive, therefore they are activated by the electromagnetic fields generated by nearby readers.
Easy tutorial about hacking our first MIFAR/RFID Tag. RFID is a technology widely used in our lives, from our building access badges, to payment facilities, or even our gates’ remotes. As we’ve seen in the previous post here, some of them are utilizing little to no security mechanisms, like MIFARE.
rfid scammers
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and can sniff and log. RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards. The technique is a collection of security vulnerabilities that would allow a hacker to almost instantly open several models of Saflok-brand RFID-based keycard locks sold by the Swiss lock maker. Step-by-Step Tutorial: How to Copy or Clone Access Cards and Key Fobs Access credentials are prone to hacking. This post explains how easy it is to copy access cards with Flipper Zero, off-the-shelf hardware, and an app. 10 min reading time
Hacker Tool Teaches All About NFC And RFID. The Flipper Zero is a multipurpose hacker tool that aims to make the world of hardware hacking more accessible with a slick design, wide array of . As detailed in the report, the security vulnerability allows “card-only” attacks, requiring access only to a card and not the corresponding card reader. The hackers can read and write data in just a few minutes of physical proximity .
There are many access control systems that rely on UID to authenticate and grant access. Sometimes this happens even when RFID tags support cryptography . Such misuse brings them down to the level of the dumb 125 kHz cards in terms of security .
In their popular talk at 24C3, punctuated by bursts of raucous applause, Nohl presented an overview of radio frequency identification security vulnerabilities and the process of hacking the. Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. Some tags are passive, therefore they are activated by the electromagnetic fields generated by nearby readers.
rfid scam
Hold your Octopus and NFC-enabled Android mobile device steady while trying to read the Octopus card. For iOS mobile devices: iPhone 7 or newer with iOS 13 or above: Pls try holding the card about 1-2cm away from your phone. Hold your .
rfid access card hack|rfid scammers